Cybersecurity
Tag
Data Breach
Cybersecurity
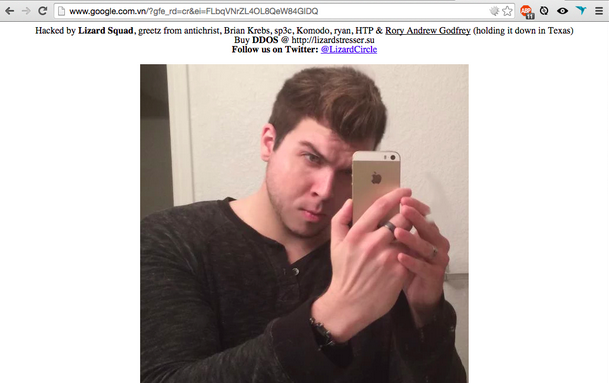
The growing threat of DDoS attacks on DNS
Cybersecurity
What businesses should expect from cyber threats in 2015
Cybersecurity
How do you solve a problem like cybercrime?
Cybersecurity
Cyber security in law firms
Recommended Content
Partner Content
Is your business ready for the IDP revolution?
Partner Content
Tips for making sure your AI-powered FP&A efforts are successful
Partner Content