Cybersecurity
Tag
Threat Detection
CIO and CTO
Kim Anstett appointed new CIO of Trellix
Cybersecurity
ExtraHop names Patrick Dennis as new CEO
Cybersecurity
93% of SOCs implementing AI and ML for threat detection
Cybersecurity
Why SOAR will revitalise the SIEM market
Communications & Networking
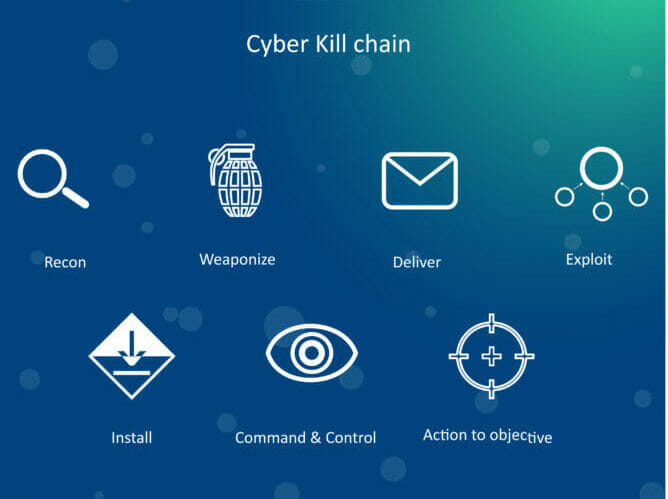
Why detection is the most critical part in the kill chain
Recommended Content
Partner Content
Is your business ready for the IDP revolution?
Partner Content
Tips for making sure your AI-powered FP&A efforts are successful
Partner Content